EDR, CVE, SIEM, ATP, XDR… Are you trying to improve your company’s IT security, but getting lost in a flood of acronyms? Entering the cybersecurity field is a big challenge, and its complexity can be off-putting to many. What is thoughtful marketing and what are the technologies fundamentally impacting your level of security?
Cybersecurity must be built on a strong technology foundation, closely followed by the management and governance services of the deployed technology solutions. Following the security pyramid scheme, you systematically build your cyber resilience from the ground up with expert services. In putting together the different levels, consideration is given to the aspects that are expected from the companies’ perspective – importance and relevance in achieving security, the best possible price/security ratio, as well as the complexity of the solution and the associated need for advanced expertise. How to build and understand security level by level?
What is cybersecurity and what is its complexity?
Cybersecurity is the activity of protecting computers, servers, mobile devices, electronic systems and data. Cybersecurity includes any aspect of protecting an organization and its employees from cyber threats. With the ever-increasing sophistication of cyber attackers and the growing complexity of corporate networks, a spectrum of security solutions are necessary to mitigate risk, including: endpoint security and management, network security, application security, information security, operational security, cloud security, end-user education, and more. In addition to technology, cybersecurity also includes people, processes and policies.
Given the sophistication of the attackers and the techniques used, cybersecurity must focus holistically on the entire organisation – all of its devices, networks, access points, technologies, data flows, processes, policies and employees, as each point represents a potential risk and a point of penetration for an attacker into the organisation.
Why are attackers interested in small and medium-sized businesses?
Cyber criminals always try to take the path of least resistance, where they try to maximize profit with the least amount of energy, time and money. While targeted, dedicated attacks on large multinational companies may look tempting at a ransom of a few million Euros, this is not actually the case. Individual dedicated attacks must break through advanced technology solutions managed by security experts, backed by a range of security policies and measures. The resulting cost vs. benefit ratio is relatively low.
Automated, large-scale attacks with advanced, easily replicable techniques and methods that exploit system vulnerabilities provide a much better ratio. Due to low cybersecurity budgets, small businesses do not have the opportunity to take advantage of the latest technologies, which are handled by security specialists. This makes them much more vulnerable and therefore more interesting to cyber criminals. It is therefore no wonder that small and medium-sized businesses are the target of more than 70% of all attacks.
How can small and medium-sized enterprises defend themselves effectively?
The main prerequisite is to build a long-term security strategy, systematically building on solid foundations, progressively evolving into more advanced technologies and security measures.
Don’t be tempted by nice-sounding abbreviations and acronyms!
It goes without saying that every technology company wants to showcase its most advanced solutions at the frontiers of current capabilities and knowledge. In any case, the presentation must not miss any mention of artificial intelligence, machine learning, automation, threat hunting and describing the technology as “next generation”. Of course, when it comes to expert “state of the art” technologies and tools, these are just the expensive icing on the cake for organisations that have basic security well covered.
Where and how to get started with cyber security?
For a simple graphical representation of a systematic approach to building security, we have developed the concept of a security pyramid composed of four levels.
- The first level represents basic, often passive security;
- The second level represents enhanced security and basic monitoring;
- The third level includes professional security, active monitoring and security management;
- The fourth, highest level represents the so-called “state of the art” advanced specialised technologies and services for the comprehensive protection of large organisations.
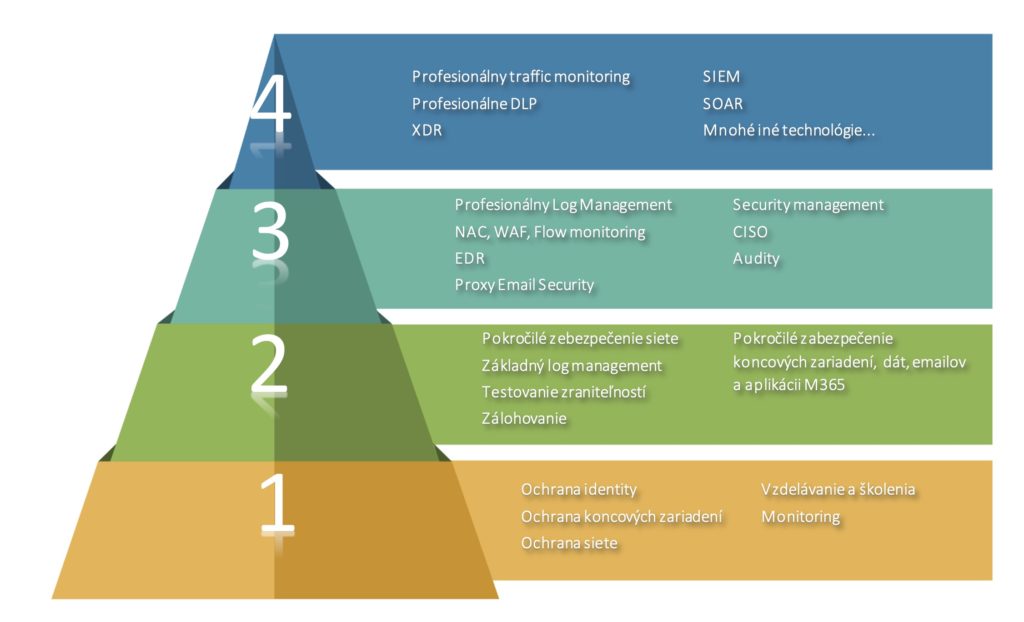
A closer look at the levels of the security pyramid
Level 1
The lowest level includes the bare minimum necessary for any company, employee, and each of us in our personal lives. Level 1 technologies and products require professional implementation and setup, but do not require active management. Thus, the expertise and competency requirements for managing such a solution are significantly lower, and a single security specialist is able to cover the spectrum of these technologies at a basic level.
Level 2
The second level still consists of a group of basic security measures and technologies, very important for any small business. In addition to the ability to deploy more advanced and complex policies, the fundamental difference is the level of interaction required to manage the security solution. From the second level onwards, it is important to understand that the job does not end with the implementation of security measures. As the level of security technology grows, the complexity, the demands for expertise, and most importantly the level of interaction and activity required on a daily basis grows exponentially. Even the second level requires at least one security specialist to actively monitor and manage the security solution.
Level 3 and 4
Higher level technologies and services are state of the art – advanced solutions at the edge of current technological and security capabilities. However, the problem is their complexity, which prevents their active use by the customer himself, who does not have security specialists with deep specialized knowledge and experience. The need for expertise, knowledge and competence is growing exponentially, which is why level 3 and above is beyond the expertise of the vast majority of companies. Advanced solutions require not only independent security experts, but as the level rises, so does their high level of specialization in specific solutions, products or vendors.
Therefore, we must reiterate that the implementation, configuration, active monitoring and management of advanced security solutions such as EDR, XDR, SIEM and many other Level 3+ solutions require dedicated cybersecurity specialists. Otherwise, there can be a sense of false security resulting from the purchase of expensive professional licenses and technologies, without their professional deployment, debugging, constant active assessment of warnings and alerts, you end up with a lower level of actual security than with professionally deployed tier 1 and tier 2 solutions.
I am a small to medium sized business, which parts should I focus on?
Above all, cybersecurity must be based on a strong technological foundation. This basic level of security is relevant regardless of company size, segment and focus. Even the most advanced security strategy stands on the same solid foundation.
For any small to medium sized business, we recommend focusing on tier 1 and tier 2, whose professional design, implementation and subsequent management will protect the customer from the vast majority of attacks.
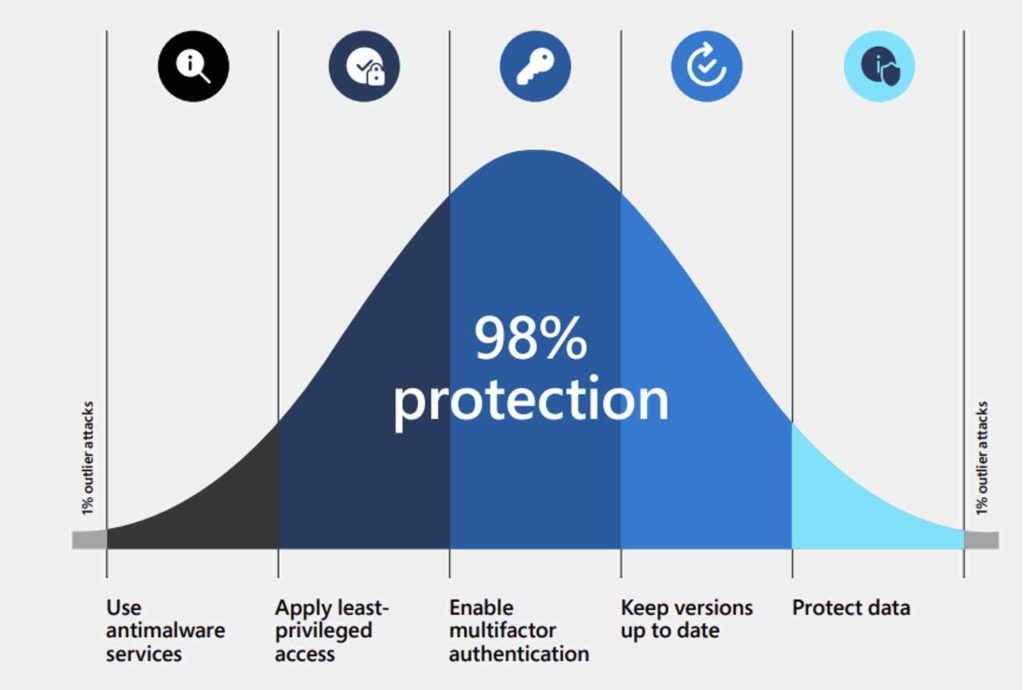
What cybersecurity leaders have to say
In an April 2022 Microsoft document, you will read, “It is a common perception that cyberattacks are complex and difficult to stop. But the reality is that most attacks are the fault of employees ignoring basic security practices. Even state-sponsored hacking involves a set of basic simple tactics in most cases.”
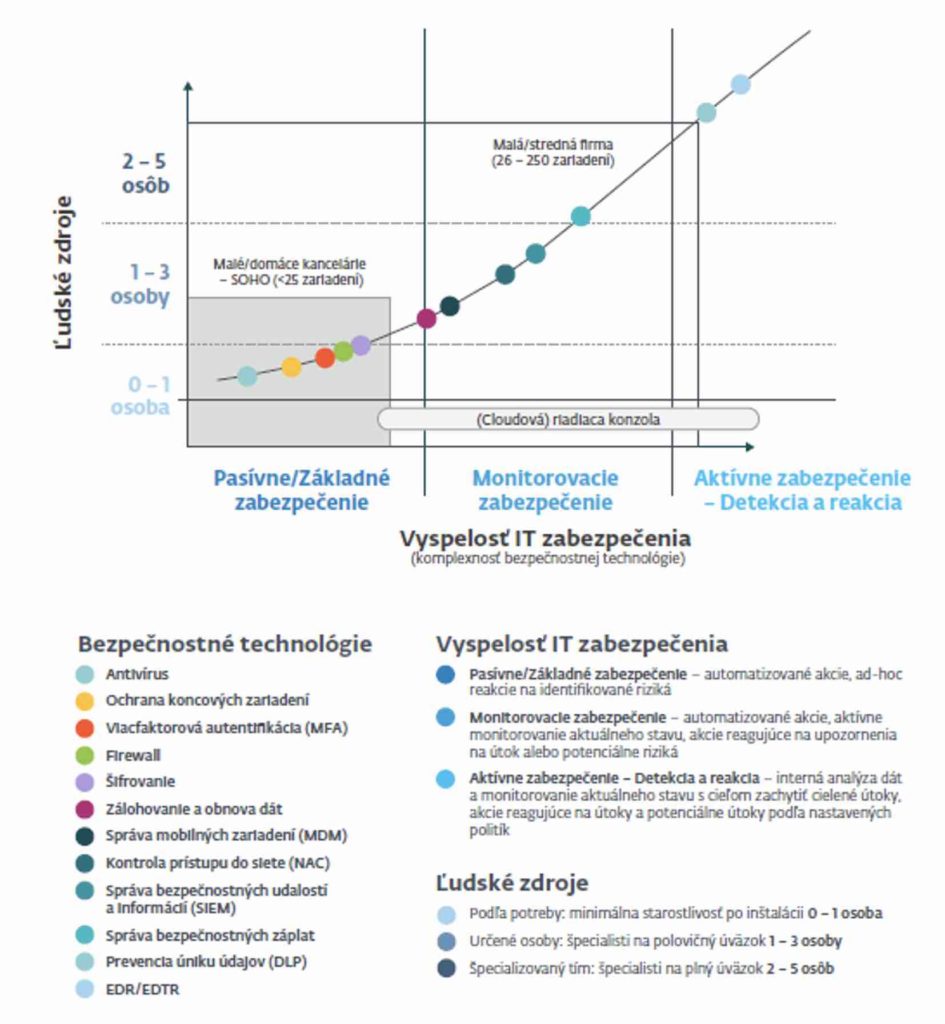
ESET has a very similar view on the issue and classification of security measures for small and medium-sized companies, the graphical representation of which can be seen in the following figure.
Need advice?
We’re here for anyone who is serious about cyber security. Whether you need to deploy antivirus on your endpoints or desire professional security backed by a SIEM, our specialists will custom build expert consolidated solutions from world-class vendors.
We’ll help you navigate through the flood of nice phrases, acronyms and acronyms and together we’ll develop the optimal solution with the best price/safety ratio.








